API Authentication
API authentication is a crucial process that verifies the identity of users or applications attempting to access an API. It ensures that only authorized entities can interact with the API, safeguarding sensitive data and functionalities from unauthorized access. Various authentication methods exist, including username-password combinations, API keys, and token-based systems like JSON Web Tokens (JWT). Each method has its own strengths and weaknesses, making it essential for developers to choose the right approach based on their specific use case. Proper implementation of authentication not only enhances security but also builds trust between users and the services they access.

API Security Essentials: Comprehensive Practices to Safeguard Your Data Exchange
Introduction In today’s interconnected world, where data exchange between applications and services is commonplace, the security of APIs (Application Programming Interfaces) is paramount. APIs serve a...
📚 Read more at Level Up Coding🔎 Find similar documents

API Authentication with Tokens
In this article I'm going to show you a few common patterns for client authentication based on tokens, and how can they be implemented in a Python API back end. This method of authentication works…
📚 Read more at Miguek Grinberg Blog🔎 Find similar documents
API Authentication Explained: API Keys, JWT, and OAuth (Without the Boring Jargon)
From every time you check your bank balance, send a message over WhatsApp, or get directions using Google Maps, APIs are doing the unseen work in the background. However, before it provides that sweet...
📚 Read more at Javarevisited🔎 Find similar documents

Auth Schemes of REST API
The user’s data is the underlying currency that is driving the API economy. Like any currency, you need to handle it with care and transport it with caution to prevent theft. Different devices and…
📚 Read more at Towards Data Science🔎 Find similar documents
API Authentication with Laravel + JWT
Authentication is a basic feature of most services on the internet. We want to be able to restrict who has access to what, and to do it in the most convenient and secure way possible. This article…
📚 Read more at Level Up Coding🔎 Find similar documents
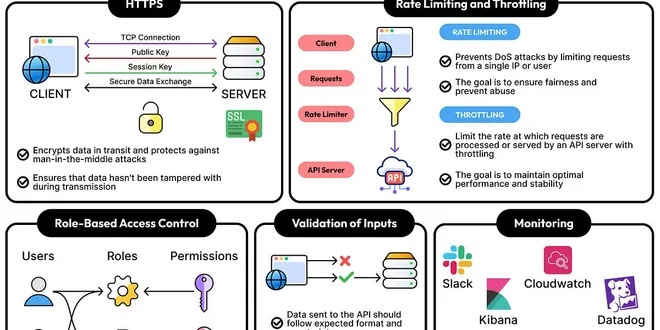
How to Implement API Security
Most APIs that ship to production have some security in place. Most of the time, HTTPS is enabled, an API key is required, and maybe there’s even a quick code review before deployment.
📚 Read more at ByteByteGo Newsletter🔎 Find similar documents
Spring Boot — Securing API with basic authentication
Spring Boot — Securing API with basic authentication Introduction : In today’s article, we will discuss what is basic authentication and securing spring boot rest APIs using basic authentication. Pre...
📚 Read more at Javarevisited🔎 Find similar documents
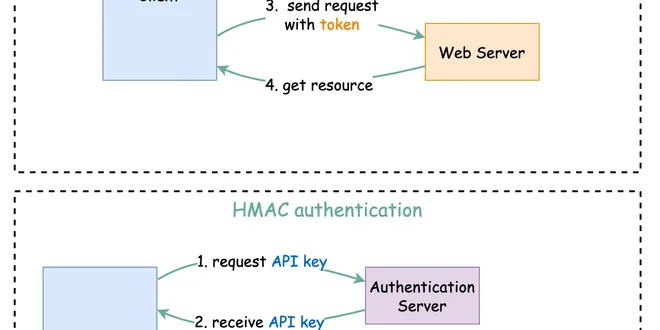
How to design a secure web API access for your website?
How to design secure web API access for your website? When we open web API access to users, we need to make sure each API call is authenticated. This means the user must be who they claim to be. In th...
📚 Read more at ByteByteGo Newsletter🔎 Find similar documents
Middleware Shield: Building Secure APIs with .NET Core Authentication
Today I’d like to share a straightforward way to secure your API endpoints using API key authentication in a .NET Core 7 environment. API security is a cornerstone of modern software development and e...
📚 Read more at Level Up Coding🔎 Find similar documents
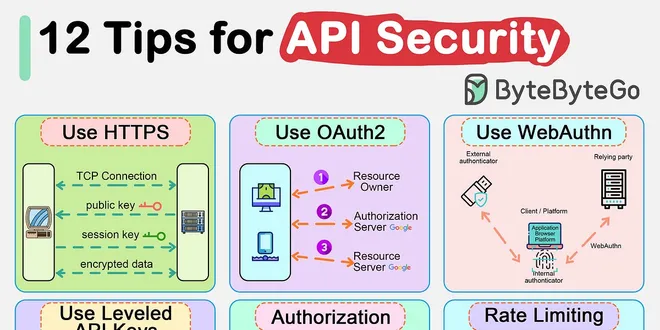
API Security Best Practices
APIs are the backbone of modern applications. They expose a very large surface area for attacks, increasing the risk of security vulnerabilities. Common threats include SQL injection, cross-site scrip...
📚 Read more at ByteByteGo Newsletter🔎 Find similar documents
Creating Secure API’s with EasyAuth & FastAPI
Currently the API is accessible and usable by anyone with a network connection that can reach the server: Instead of re-creating users, group, roles, & permission, centralize into a single auth…
📚 Read more at Analytics Vidhya🔎 Find similar documents
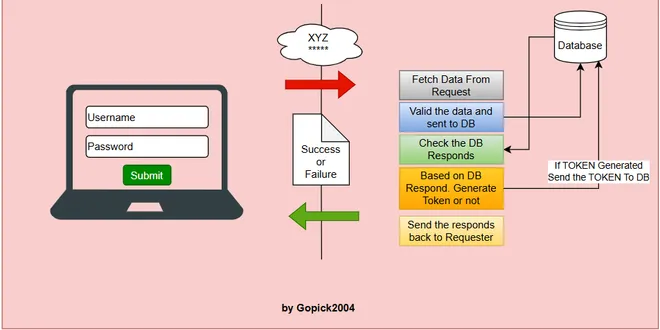
Building a Simple Login API with Spring Boot: My Step-by-Step Guide
Not a member read it here What Is a Login API? A login API is a service that accepts user credentials — like a username and password — and validates them. If the credentials are correct, the API retur...
📚 Read more at Javarevisited🔎 Find similar documents


