Adversarial Training
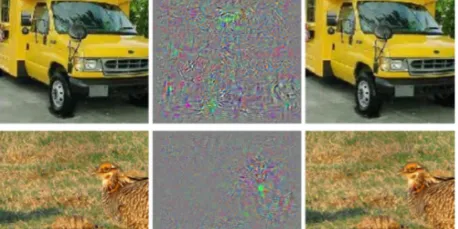
Adversarial training is a crucial technique in machine learning aimed at enhancing the robustness of models against adversarial examples—inputs intentionally designed to deceive the model. This approach involves incorporating adversarial examples into the training process, allowing the model to learn from these challenging inputs. There are two primary methods: one involves retraining the model with previously identified adversarial examples, while the other integrates perturbations directly into the training process. By doing so, adversarial training not only improves the model’s accuracy but also its generalization capabilities, making it more resilient to various types of adversarial attacks.
Everything you need to know about Adversarial Training in NLP
Adversarial training is a fairly recent but very exciting field in Machine Learning. Since Adversarial Examples were first introduced by Christian Szegedy[1] back in 2013, they have brought to light…
📚 Read more at Analytics Vidhya🔎 Find similar documents


