Web Security
Web security is a critical aspect of protecting websites and web applications from various threats and vulnerabilities. It encompasses a range of practices and technologies designed to safeguard sensitive data, ensure user privacy, and maintain the integrity of online services. Common threats include cross-site scripting (XSS), cross-site request forgery (CSRF), SQL injection, and session hijacking, which can compromise user accounts and sensitive information. Implementing robust security measures, such as proper input validation, data encryption, and regular security audits, is essential for defending against these attacks and ensuring a safe online experience for users.
Web Application Security
Web applications can be attacked many ways by malicious actors. Learn more on Full Stack Python.
📚 Read more at Full Stack Python🔎 Find similar documents

Security Considerations
Security Considerations Web applications usually face all kinds of security problems and it’s very hard to get everything right. Flask tries to solve a few of these things for you, but there are a cou...
📚 Read more at Flask User's Guide🔎 Find similar documents

Security Considerations
Security Considerations Web applications usually face all kinds of security problems and it’s very hard to get everything right. Flask tries to solve a few of these things for you, but there are a cou...
📚 Read more at Flask User's Guide🔎 Find similar documents

Security
No security is perfect, but there’s a number of important restrictions built into MashProxy and SearchMash. The security in MashProxy is based around the Java applet being digitally signed. This signa...
📚 Read more at Pete Warden's blog🔎 Find similar documents
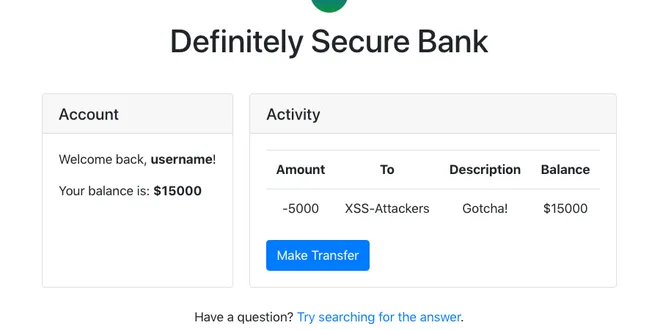
Web Security 101: Cross-Site Scripting (XSS) Attacks
A hands-on beginner's guide to what XSS attacks are and how to prevent them.
📚 Read more at victorzhou.com🔎 Find similar documents

Security Intro
Security Intro There are many ways to handle security, authentication and authorization. And it normally is a complex and "difficult" topic. In many frameworks and systems just handling security and ...
📚 Read more at FastAPI Documentation🔎 Find similar documents

OWASP: Introduction to Web Application Security
OWASP | Security | Django| Web Development
📚 Read more at Level Up Coding🔎 Find similar documents

10 security tips for frontend developers
Web security is a topic that is often overlooked by frontend developers. When we assess the quality of the website, we often look at metrics like performance, SEO-friendliness, and accessibility…
📚 Read more at Level Up Coding🔎 Find similar documents

Web Security: What Is XSS?
A Cross-Site Scripting attack, or XSS for short, is a type of cyber attack that uses malicious scripts to inject into webpages. These… Continue reading on Level Up Coding
📚 Read more at Level Up Coding🔎 Find similar documents

Security
Most Django applications contain a lot of proprietory or even confidential information. Hence, it is crucial to take all possible measures to take your Django application secure and to recude the pos...
📚 Read more at Python Anti-Patterns🔎 Find similar documents

How to secure your web service
Photo by Karl Randay If you're including third-party content in your web pages, you can't stop a determined attacker. Browsers weren't designed with that scenario in mind, so by default any HTML you p...
📚 Read more at Pete Warden's blog🔎 Find similar documents

9 Security Implications to Consider Before Deploying a Web App
Security checklist to protect web applications and Restful services against the most common attacks based on OWASP Top 10 Web Application Security Risks
📚 Read more at Better Programming🔎 Find similar documents


